Introducing RKE Government: Security-Driven Kubernetes Engine
October 31, 2020.
Today, Rancher Labs and Rancher Federal are announcing a new open-source project, RKE Government, a new, easy-to-install Kubernetes distribution specifically engineered to adhere to the robust security requirements of public sector organizations. To meet the needs of Rancher Federal’s growing number of US federal customers, our engineering teams built a highly secure, FIPS-enabled Kubernetes distribution called RKE Government (FIPs stands for Federal Information Processing Standards).
This new fully CNCF-certified Kubernetes distribution combines the data center scalability of RKE with the flexibility of K3s to deliver secure workloads across any infrastructure — cloud-connected, on-premise, or even air gap.
RKE Government adds several security enhancements to Rancher’s catalog, including Security-Enhanced Linux (SELinux) via containerd (an industry first) and the first fully FOSS FIPS-140-2 validated Kubernetes encryption module.
In close collaboration with Rancher Federal, Rancher Labs built RKE Government to be the next evolution of their Kubernetes engines. By combining the data-center scalability of RKE, the flexibility of K3s, and wrapping them both in armor, we have created RKE Government.
How is RKE Government different from RKE or K3s?
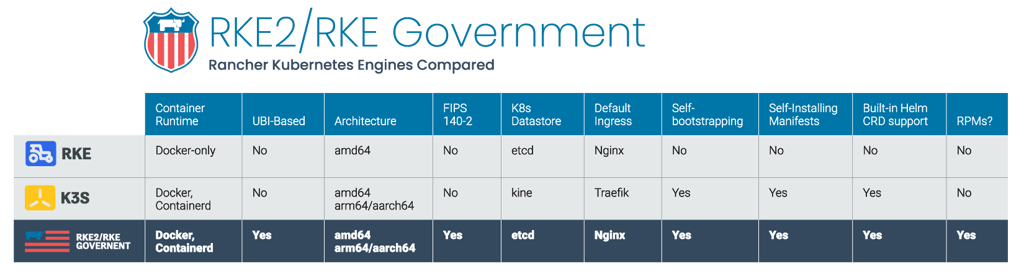
RKE Government combines the best of both worlds from the 1.x version of RKE (hereafter referred to as RKE1) and K3s.
From K3s, it inherits the usability, ease-of-operations, and deployment model.
From RKE1, it inherits close alignment with upstream Kubernetes. In places, K3s has diverged from upstream Kubernetes to optimize for edge deployments, but RKE1 and RKE Government can stay closely aligned with upstream.
Importantly, RKE Government does not rely on Docker as RKE1 does. RKE1 leverages Docker for deploying and managing the control plane components as well as the container runtime for Kubernetes. RKE Government launches control plane components as static pods, managed by the kubelet. The embedded container runtime is containerd.
FIPS-140-2 without the Pay-wall
The ever-evolving mission of the United States government demands security at every layer of the software stack. To help harden the footprint of software operations, numerous security controls must be enforced to pass rigorous compliance checkpoints and help achieve an ATO (Authority To Operate). Many of the most sensitive missions that Rancher Federal supports require FIPS-140-2 encryption modules, demanding mission-grade encryption both in the datacenter and beyond. Rancher Labs and Rancher Federal are proud to announce that they have produced Rancher Kubernetes Cryptographic Library, the community’s first free and open source (FOSS) FIPS-140-2 Kubernetes encryption module at the core of RKE Government. Rancher has worked closely with CoreSec and the NIST National laboratories to deliver an encryption module that can drive your cloud-native Kubernetes from the datacenter to the tactical-edge. RKE2 and the components it deploys (with the exception of NGINX ingress) have been compiled to leverage the FIPS 140-2 validated BoringCrypto module.
NIST: Rancher Kubernetes Cryptographic Library
SELinux & CIS Kubernetes Security Benchmark
Continuing with the “secure all the things” mantra of RKE Government, we are proud to announce that we are extending SELinux support to include the containerd container runtime. While the Docker runtime has previously supported SELinux hardening, our engineers contributed this functionality back into the containerd project starting in 1.4. This capability will allow secure Kubernetes workloads to run under SELinux enforcement mode no matter the container runtime that their mission demands.
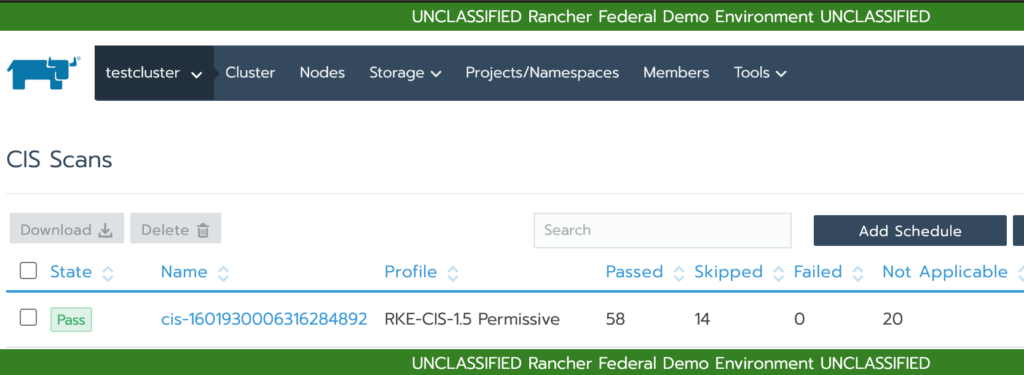
A system can only be classified as secure after it passes rigorous testing. The Center for Internet Security (CIS) is a 501©(3) nonprofit organization, formed in October 2000, with a mission is to “identify, develop, validate, promote, and sustain best practice solutions for cyber defense and build and lead communities to enable an environment of trust in cyberspace”. CIS Benchmarks are best practices for the secure configuration of a target system. CIS Benchmarks are developed through the generous volunteer efforts of subject matter experts, technology vendors, public and private community members, and the CIS Benchmark Development team. RKE Government is built to run in a hardened mode that is designed to pass CIS’ most rugged security standards. Contributing to your enterprise’s automated-compliance strategy, RKE Government seamlessly integrates with Rancher’s built-in CIS scanning functionality. This enables your operations team to be notified of any CIS security abnoralities and deliver automated security scans to your team in a highly dynamic secure manner.
RKE Government = RKE2
Some users may be wondering why this new distribution is referred to as RKE2 rather than RKE Government on GitHub and in the documentation.
The name ‘RKE Government’ conveys the primary use cases and market it currently targets. However, in the development of RKE Government, we determined that the broader community would benefit from many of the security-centric capabilities that we initially targeted for the US government. Once we’ve completed an upgrade path and Rancher-integration feature parity work is ready, RKE1 and RKE Government will converge into a single Kubernetes distribution – RKE2.
Getting Started
1. Run the Installer
curl -sfL https://get.rke2.io | sh -2. Start the rke2-server
systemctl start rke2-server.service3. Follow the logs, if you like
journalctl -u rke2-server -f4. Enjoy your new Kubernetes cluster
KUBECONFIG=/etc/rancher/rke2/rke2.yaml kubectl get allConclusion
We are excited to release RKE Government today to the world. This is not just a new chapter of Kubernetes within the US government, but a slingshot of security for the entire Kubernetes community. RKE Government is now available for amd64-based RHEL/CentOS 7, RHEL/CentOS 8 and Ubuntu systems. RKE Government is the simplest, most secure Kubernetes distribution in the community today — and we’re just getting started. Stay tuned.